Two Key Differences Between Digital Forensic Imaging And Digital Forensic Clone And How They Can Affect Your Legal Case.
Written By
What is a Forensic Image? What is a Clone? How is a Forensic Image different than a Clone? These are questions that we address frequently at Capsicum. Though on its face this would seem to be easily answered, it is much more nuanced than you might imagine. Over the years there have been many terms used to describe a Forensic Image versus a Clone and the process of making a forensic backup. Terms such as mirror image, exact copy, bit-stream image, disk duplicating, disk cloning, and mirroring have made it increasingly difficult to understand what exactly is being produced or being requested.
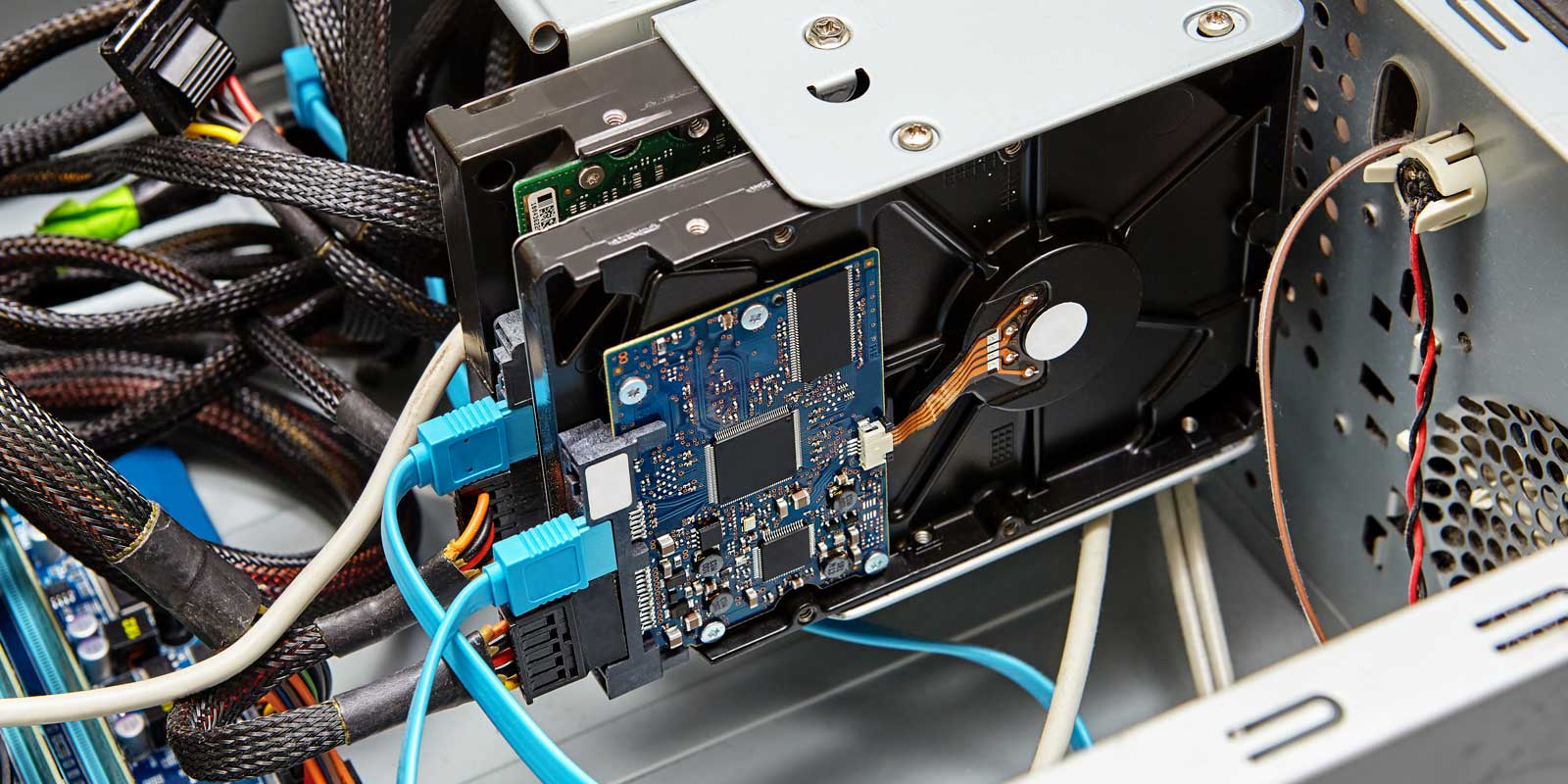
Broadly speaking, forensic backups are achieved by capturing all data from a source media (computers, cell phones, tablets, etc.) in a forensically sound manner so that all of the original data is an unaltered state. This means the entire contents of the source media are being collected, including unused space, all slack data, all unallocated space, and other medias.
How do you distinguish an Image and a Clone?
A Forensic Image is a comprehensive duplicate of electronic media such as a hard-disk drive. Artifacts (Information or data created as a result of the use of an electronic devices that show past activity) such as deleted files, deleted file fragments, and hidden data may be found in slack (Unused space that is created between the end-of-file marker and the end of the hard drive cluster in which the file is stored and unallocated space (The unused portion of a hard drive). This exact duplicate of the data is referred to as a bit-by-bit copy of the source media and is called an Image. Images are petrified snapshots, that are used for analysis and evidence preservation. Images cannot be used as working copies.
A Forensic Clone is also a comprehensive duplicate of electronic media such as a hard-disk drive. Artifacts such as deleted files, deleted file fragments, and hidden data may be found in its slack and unallocated space. This exact duplicate of the data is referred to as a bit-by-bit copy of the source media and is called a Clone. Clones are working snapshots, that are modifiable and not necessarily preserved. Clone are used as working copies to replace original evidence for analysis as well as data preservation purposes.
A hash (An error detection scheme which performs calculation on the binary value of the packet/frame and then which is appended to the packet/frame as a fixed-length field. Once the packet/frame is received a similar calculation is performed. If the result does not match the first calculation then a data change occurred during transmission. The calculation can be a sum (Checksum), a remainder of a division or the resulting of a hashing function) of an original device can validate if media is an exact duplicate (forensically sound copy). Any variation in the hash value of an original to its Clone or Image will confirm that they are not exact copies. This is of importance to know when dealing with legal matters.
Why does it matter at your law firm for a legal case?
While a Clone can be used for digital forensic analysis, it is typically used to create working copies or exact replacement drive.
Images are primarily used to forensically analyze and to preserve original data. They are petrified and in their Image format cannot be modified.
Capsicum recently had a case very closely related to this topic. An attorney was led to believe an Image and Clone were the same. The attorney asked for an Image so they could review files from a computer. Capsicum experts held a requirements gathering meeting and were able to get to the root of what work products were required. We were able to explain that without forensic tools the Image was not readable. We further explained that while a Clone could be reviewed and searched, original data would be modified. In the end, after collaborating with the attorney, we produced both Clone and Image. At Capsicum, we provide deep technical expertise and are well versed in leading or participating in your electronic investigation.
No matter the level of complexity, Capsicum Groups’ team of tech and legal experts is equipped with the leading-edge technology and intensive strategies for your success. Learn more about our forensic recovery and cybersecurity services in Philadelphia, New York, and South Florida by connecting with us via our Contact page or by calling 1-888-220-3101.
Here are some additional articles written by Capsicum which you may of interest:
Just Text Me: Top 5 Questions Digital Forensics Experts Are Asked Regarding Text Message Evidence
